Protection is better than Cure
We all know that WordPress has become the most successful CMS powering almost 27% of all websites running today and thus capturing almost 76% of the CMS market share. But, even with such brilliant stats, WordPress is always widely known to be a high security risk CMS (check out our other blogs related to this). One such security risk associated with WordPress is known as Remote Code Execution (RCE).
Considering this to be an important aspect of WordPress security prevention measure, in this post, you’ll get complete and well-described solutions for Remote Code Execution (RCE) along with knowing how they impact a WordPress site.
We believe in taking proactive steps for preventing any measure disaster from undermining the performance of a WordPress website instead of curing it when it occurs.
So, let’s get preventing!!
An Introduction - What is Remote Code Execution?
According to the 2020 Global Threat Intelligence Report, “Remote Code Execution attacks – also known to most geeks, cyber specialists, and computer programmers as code injection – is the most common but lethal cyber security threat”.
Think of Remote Code Execution as an umbrella term covering a variety of WordPress hacking methods. Following are the most common types of remote code execution attacks:
- Type Confusion – A type of RCE attack in which a piece of code doesn’t validate an object’s integrity and makes it easy for hackers to inject commands to create a mismatch in object types.
- SQL Injections – It enables hackers to tamper with queries as they are free to inject malicious statements into a database.
- Deserialization – Before knowing about ‘deserialization as a threat’, let’s understand what is ‘serialization’? A serialization is the process to convert complex data structures i.e., fields and objects into format for restoring later. Serialization makes it easy to write complex data for inter-processing a database, a file or a memory, and it gets easy to send complex data in an API call, etc. Coming back to deserialization – it is one of the types of remote code execution attacks in which an untrusted data is used for inflicting a code execution by bypassing authentication and disfiguring an application’s basic logic.
- Cross-Site Scripting (XSS) – In this attack a hacker injects unauthorized JavaScript code to exploit vulnerability in your website.
What are the Three Methods to Protect Your Website From Remote Code Execution?
Remote Code Execution (RCE) attacks can affect a WordPress site in various ways. For instance, they can steal private and confidential data of customers or can put your server offline which can ultimately destroy the reputation of an online business badly. For this purpose, it’s highly indispensable for you to understand how to protect your website from Remote Code Execution (RCE).
We have identified three methods that are highly effective against Remote Code Execution. These methods are as follows:
Method # 1: Ensure Your Website and Extensions are Continuously Monitored and Upgraded
The first and easiest to protect your WordPress website from remote code execution is to ensure that you are monitoring WordPress security in all extensions, tools and systems that are being used by the website. WordPress brings out constant and periodic updates to its version especially in the security department pertaining to themes and plugins to fix any security issue.
Therefore to ensure that all the things associated with WordPress website are upgraded on a timely manner will prevent any RCE threat.
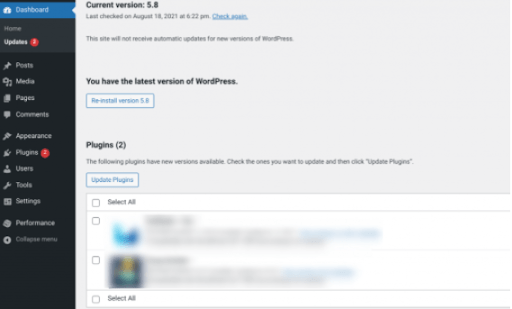
That’s why we recommend that you have a proper team to handle the WordPress website monitoring so that if any new update is released, it is implemented in a timely manner because the risk of security increases.
Method # 2: Install a WAF (Web Application Firewall) to Avoid Remote Code Execution
Another step that you can take to safeguard your WordPress site from Remote Code Execution is to use Web Application Fire (WAF).
WAF filters out suspicious requests before they damage your site. In other words, it adds an extra layer of protection or shield between a web server and the incoming traffic. WAFs make your site well-protected so that you can keep bad actors away from wreaking havoc on your WordPress site. You can use the Sucuri WAF services to protect your WordPress website.
Sucuri WAF not only protects your WordPress website from remote code execution but protects it from other security threats i.e., DDoS (Distributed Denial-of-Service) attacks.
Method # 3: Use Professional Malware and Infection Removal Services to Safeguard your Website
Another method to ensure top-level security is to actually hire a professional malware and infection removal service.
Using a professional team simplifies the monitoring and security of the WordPress website by ensuring that they do all the hardwork for you while you have a good night’s sleep without having to worry about the performance of your WordPress website. The team ensures that all private and confidential files are clean and safe from all types of threats by doing continuous scans all of your site all at once, analyzing key-security information, and maintaining logs of all past security scans.
So What will you Choose - Early Protection or an After Cure for Remote Code Execution Threat?
Fail-proof security of a website should be your top priority because it helps prevent security breaches and attacks such as Remote Code Execution. Therefore, you should apply inevitable security precautions, otherwise, you can become a victim of hackers, in no time.
If you have any questions, feel free to reach out to us and our experts will be happy to help without costing you a penny.
